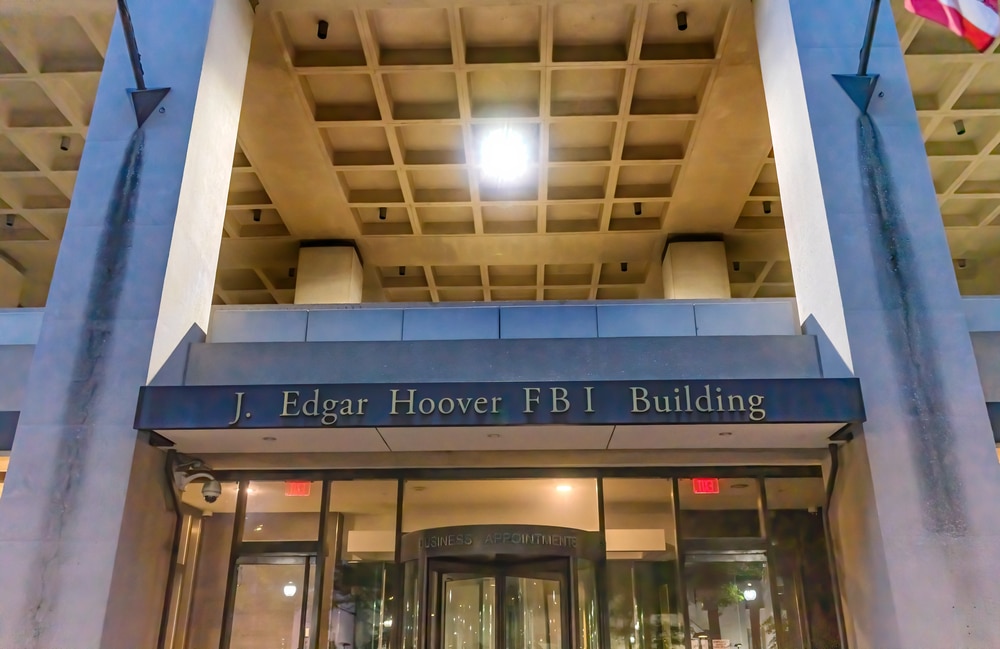
Chinese government hackers are suspected of breaching the FBI’s Digital Collection System Network (DSCNet), the internal infrastructure the bureau uses to manage court-authorized wiretaps and foreign intelligence surveillance requests, according to one congressional aide and two U.S. officials with knowledge of the matter.
The FBI determined the intrusion meets the definition of a major incident under the Federal Information Security Modernization Act (FISMA), a threshold that requires agencies to notify Congress within seven days of finding that a breach is “likely to result in demonstrable harm” to U.S. national security.
Congress was informed of that determination the week of March 17, according to the congressional aide.
The specific system targeted was DCS-3000, an unclassified component of DSCNet known internally as Red Hook, which processes pen register and trap-and-trace surveillance operations.
Those tools collect call metadata, including numbers dialed, routing data, and the identities of individuals under active FBI investigation.
The potential consequence goes beyond data theft: if adversaries accessed that target list, they could identify which of their own operatives the bureau was monitoring.
“Thresholds under FISMA are quite high, and only a few agencies declare a major cyber incident every year,” said Cynthia Kaiser, former deputy assistant director of the FBI’s cyber division.
The FBI first detected abnormal log activity on February 17 and notified Congress on March 4. A notification sent to lawmakers, obtained by Politico, said hackers entered the network by “leveraging a commercial Internet Service Provider’s vendor infrastructure,” which the bureau attributed to the group’s “sophisticated tactics.”
The White House subsequently convened a meeting that included officials from the FBI, the National Security Agency (NSA), and the Cybersecurity and Infrastructure Security Agency (CISA).
No specific hacking group has been formally named. Investigators have focused attention on Salt Typhoon, a threat actor linked to China’s Ministry of State Security (MSS) that breached all three major U.S. cellular providers between 2019 and 2024, siphoning call records from tens of millions of Americans and accessing FBI wiretap infrastructure in the process.
Michael Machtinger, deputy assistant director for cyber intelligence at the FBI, said in February 2026 that Salt Typhoon threats remain “still very much ongoing.”
One U.S. official familiar with the incident said it was “embarrassing” for the bureau to be breached by the same adversary it is tasked with tracking.
“This incident is yet another stark reminder that the threat from sophisticated cyber adversaries like China has not gone away, in fact it’s growing more aggressive by the day,” said Sen. Mark Warner, the ranking Democrat on the Senate Intelligence Committee.
The investigation into the DCS-3000 breach remains active, with the FBI working alongside CISA and the NSA to determine the full extent of the counterintelligence compromise.